The LockerGoga ransomware has been targeting industrial and manufacturing companies from the beginning of 2019
Ransomware has long been the curse of the cybersecurity industry. The digital extortion activity is not new—it’s been around since about 2005, but attackers have greatly improved the schema.
Now a vile new type of ransomware known as LockerGoga is targeting industrial firms whose computers control actual physical equipment. This is enough to deeply spook security researchers.
According to security researchers, the most recently discovered strain of the malware is particularly disruptive, shutting down computers entirely, locking out their users, and providing the difficulties for victims to even pay the ransom. The result is a dangerous combo: First – hacking that targets a set of companies that are highly encouraged to quickly pay the ransom, and second the scary fact that a cyberattack could wind up physically harming equipment or even a company’s staff.
As Joe Slowik says(a researcher at the security firm Dragos, which focuses on industrial control systems): “If you cripple the ability to operate an industrial environment, you’re costing that enterprise significant amounts of money and really applying pressure for every minute that loss of control continues. Unless that system is in a steady state of operation or has good physical fail-safes, you now have a process out of your control and out of view of your own eyes. That makes this extremely irresponsible and very nasty.”
Analysis of LockerGoga
According to Charles Carmakal, who leads a team of incident responders at FireEye, LockerGoga, which was named for a file path in its source code by security research group MalwareHunterTeam, remains relatively rare and targeted compared with older forms of ransomware. It’s not clear how the LockerGoga hackers are gaining initial access to victim networks, but Carmakal has found that they seem to already know targets’ credentials at the start of an intrusion, perhaps conducting the phishing attacks or by buying them from other hackers.
Once the intruders have an initial creds, they use the common hacking toolkits Metasploit and Cobalt Strike to jump to other computers on the network and also using the Mimikatz, which can pull traces of passwords out of the memory of Windows machines and allow them to gain access to more privileged accounts.
After they obtain a network’s highest privilege “domain admin” credentials, they use Microsoft’s Active Directory management tools to plant their ransomware payload on target machines across the victim’s systems. As Carmakal says, that code is signed with stolen certificates that make it look more legit one. Then- before running their encryption code, the hackers use a “task kill” command on target machines to disable their antivirus.
These measures and steps made antivirus completely useless against the infections. Then LockerGoga rapidly encrypts the computer’s files and as Kevin Beaumont(a UK security researcher, in an analysis of the Norsk Hydro attack):”On an average system within a few minutes, it is toast.”
Why so serious?
Finally, the hackers plant a readme file on the machine that lists their demands.
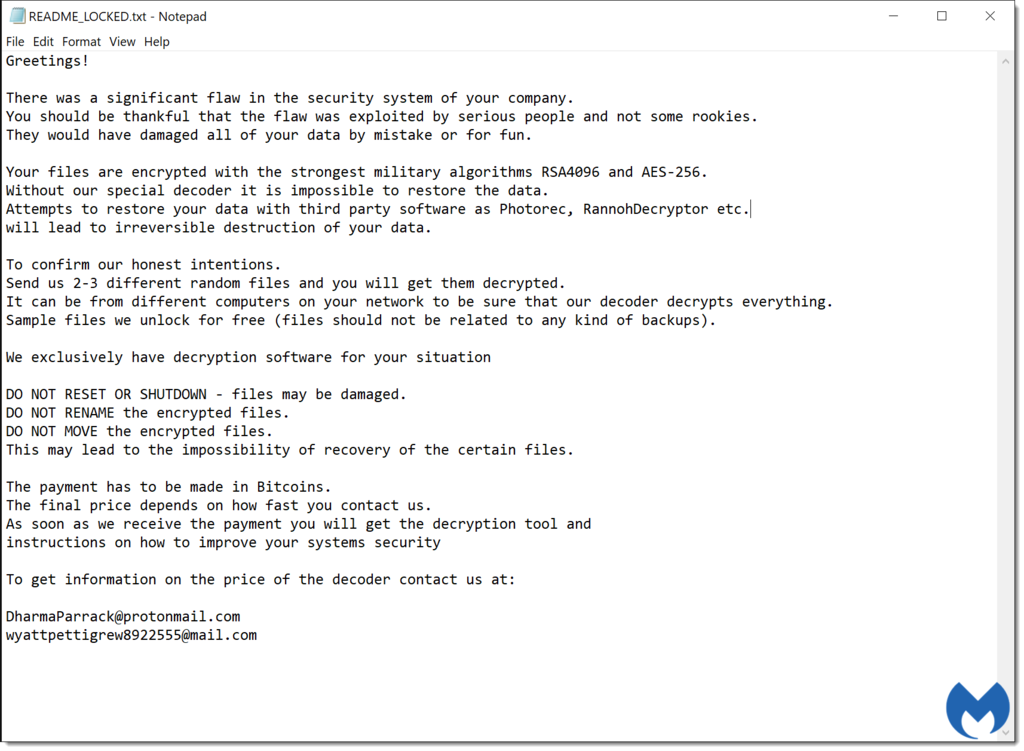
You should be thankful that the flaw was exploited by serious people and not some rookies.
However, the note doesn’t name a ransom price but it provides email addresses. In this way it demands that the victim contact the hackers to negotiate a bitcoin sum for the return of their systems.
Furthermore, researchers have analyzed that the LockerGoga also disables the computer’s network adapter to disconnect it from the network, changes the user and admin passwords on the computer, and logs the machine off.
Security researchers have found that in some cases, the victim can log back in with a particular password, “HuHuHUHoHo283283@dJD,” or with a cached domain password. However, unlike more typical ransomware, the victim often can’t even see the ransom message. In some cases, they may not even know that they’ve been hit with ransomware, delaying their ability to recover their systems or pay the extortionists, and causing even greater disruptions to their network.
Damages from ransomware attack on Norsk Hydro reach as $40M
On March 19, Aluminium company Norsk Hydro was attacked by LockerGoga and has already lost as much as $40.6 million.
Company said in a news update yesterday that most of its operations are back running at normal capacity. (good news (:)


