Privacy has a clearly defined price, and that is shown by the fact that last year certain companies offered up to $500.000 for functional zero-day exploits, which are focused on messaging applications such as WhatsApp, Telegram, Viber and Signal.
One of those companies (Zerodium) has also offered a price list, which provides a payment of half a million dollars for Remote code execution and local privilege escalation in a number of mobile messenger applications. In other words, remote code execution is the ability of the attacker to remotely execute any command on a vulnerable machine. The same approach gives the attacker the ability of elevating KERNEL, Administrator, SYSTEM or root privileges on a vulnerable system, which further increases the potential level of its exploitation.
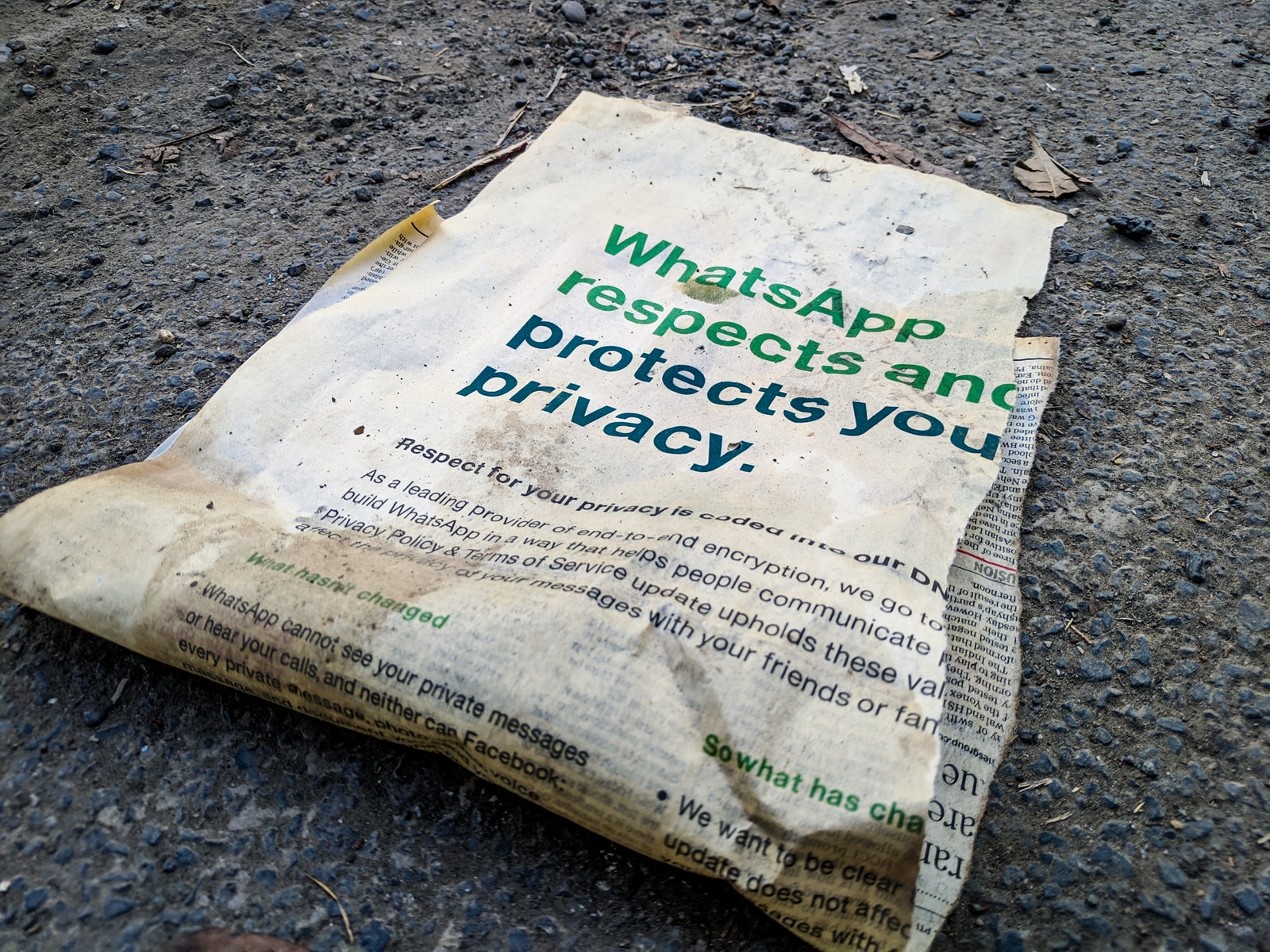
The motive that preceded the rapid increase of the “reward” for zero-day exploits has been personalized in compromising security after the companies which are offering messaging applications began introducing end-to-end encryption onto their communication lines. This kind of encryption implies that communication between users is visible only between them. That prevents interception of those lines, and the spoofing of network protocols becomes completely useless. Telephone and internet providers can no longer intercept communication between the two sides, without the cryptographic key to help decrypt the conversation or text. Companies that apply end-to-end encryption cannot submit their users’ texts of conversations to the authorities or to any third party.
From the examples provided, it is obvious that increasing customer security results in a proportionate increase of options to circumvent it from both the legal and illegal side. We most often face two perspectives; that companies and authorities with the ability of access to personal user data can prevent on time the occurrence of events that impair the security of citizens of a particular country, while advocates of the second perspective claim that the same type of approach is not optimal for increasing the safety measures, and that in this way it only violates the user privacy.
People who fully understand the issues of interception of communication and traffic are exclusively more advanced penetration testers who are able to read raw logs of TCPDUMP and are able to understand it and apply it in their practical work. Understanding of computer security for laymen is a very big issue, while a well-established minority of professionals on the other hand is not able to properly introduce even the basic skills of this type to wider masses. The problem of messaging applications is continually evolving in a negative sense, as most users have the feeling that they represent a security bubble and a free fast communication. The cruel reality of the whole situation is far more hypocritical, more ambiguous, dangerous, and more complicated than what the end users can imagine.
When, as a penetration tester, you set up an eviltwin AP at a particular location, either through some automated utility or in a more manual way using airbase-ng and simultaneous deauth or flood of a legitimate AP with authentication frames, all in order to force the users to use your wireless AP, you can notice the frustration of social network addicts who will automatically switch to your “network” even if you do not put the same SSID and BSSID. Such carelessness opens the possibility of pushing a listener inside the device that victims have, and it is possible to have shell access on them, which would circumvent any kind of encryption and protection of communications. Through this example of a properly executed action, the more experienced attackers can easily get what they want and even allow a further approach by pushing the persistent backdoor to the victim’s device. These are the capabilities of skilled individual pentesters, and just imagine the reach of the army of masters specialized in reverse engineering whose source of massive income are the companies that pay them for zeroday exploits.