Tag: security
Top Stories
SecretPixel: Securely Hide Files in Images
Unseen, Unbreakable - Secretly Hide Files in Images
NIST and EBRC Collaborate to Safeguard Synthetic Biology from AI Misuse
Building Safety Guardrails for Tomorrow's Bioengineering: NIST and EBRC Team Up.
Bruce Schneier Foresees AI-Enhanced Mass Surveillance Era
Unveiling the Future: AI and the New Age of Surveillance
Millions Exposed: Indian Data Breach Raises Global Alarm
Imagine waking up to discover your name, phone number, and address circulating among cybercriminals. This alarming reality became a nightmare…
Weaponizing Misinformation and the Need for Digital Sherlock Holmes
Is Reality Still Real? The Deepfake Dilemma.
Introduction to Docker and Security
Docker isn't going away any time soon. It's not too late to hop on the bandwagon and learn what the…
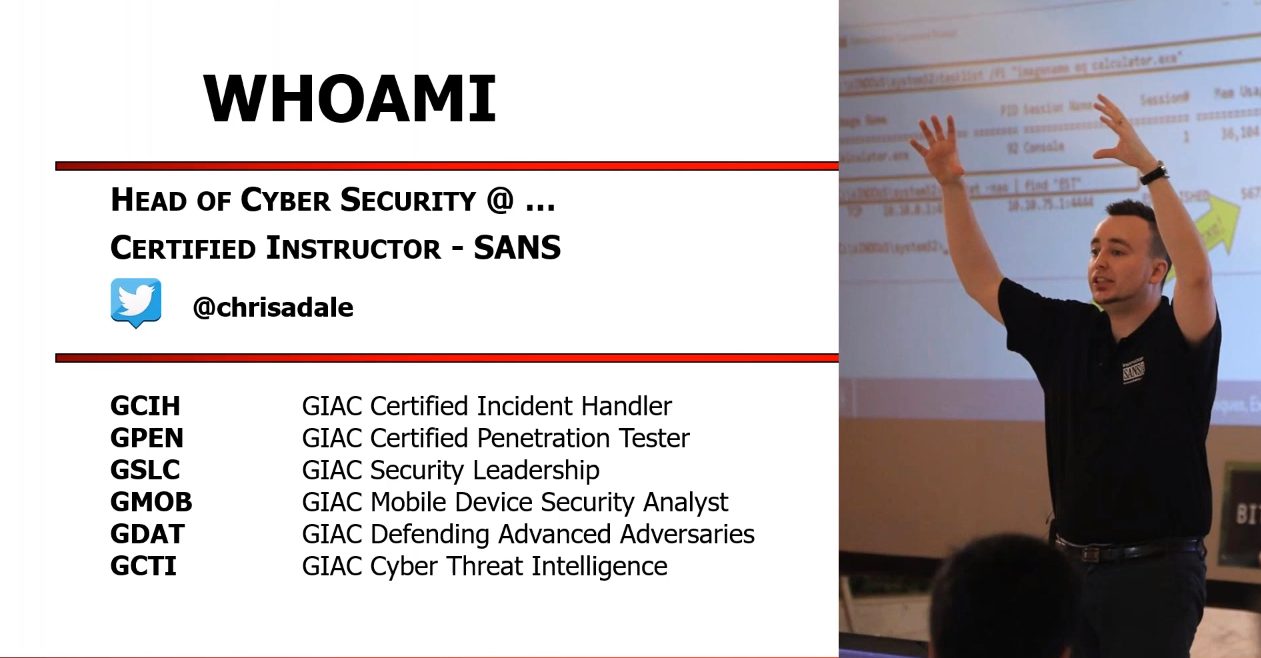
6 Popular Cybersecurity Courses
Here is the compilation of Popular Information Security Courses, Classes, Tutorials, Training, and Certification programs available online for 2019. This list…
Parrot Security OS 4.7 Beta Relased
Parrot is a GNU/Linux distribution based on Debian and designed with Security, Development and Privacy in mind. It includes a…
Brinks Home Security Is a Brand of Home Security Systems
Brinks Home Security is a professional security company which operates in most states throughout the United States. It was originally…
Top 5 Penetration Testing Tools
Penetration Testing is a method of testing in which the areas of weakness in the software systems in terms of…
What We Can Expect From Tor In 2019
The Tor Project achieved a lot in the last year. They spent 2018 fighting for the fundamental human rights to…
FaceTime group call exploit hits Apple’s iOS 12.1
Newest APPLE'S IOS 12.1 UPDATE doesn't just bring CPU throttling to the iPhone 8 and iPhone X, but also comes with a security flaw…
Fundamental Principles of Physical Security
Paradise is now shut and locked, barred by angels, so now we must go forward, around the world and see…
Situational Crime Prevention: A Philosophy of Crime Reduction
The ultimate purpose of any security system is to counter threats against assets and strengthen associated vulnerabilities. — Joseph Barry…
Android: Debugging and Analyzing Vulnerabilities
Chapter 1 - Android - Debugging and Analyzing Vulnerabilities It’s very difficult—arguably impossible—to create programs that are free of bugs.…
How Technology Impact Digital Forensics
Digital Forensics - An art form lacking broad scientific standards Forensics is changing in the digital age, and the legal…
US Navy’s Next Generation Jammers
The US Navy's Next Generation Jammer, guarantees another, more proficient warfare systems and high-power jamming through high-end military grade electronics,…
MacOS QuickLook Feature Leaks Data Despite Encryption
Specialists are advising macOS clients that not all the information they store on their encoded hard drive is secured. In…