Trape is a OSINT analysis and research tool created by Github user jofpin, which allows people to track and execute very intelligent social engineering attacks in real time.
It was created with the aim of teaching the world how large Internet companies could obtain confidential information such as the status of sessions of their websites or services and control over their users through the browser, without them knowing, but It evolves with the aim of helping government organizations, companies and researchers to track the cyber criminals.
Creator of tool – Jofpin
Benefits of the tool
- LOCATOR OPTIMIZATION: Trace the path between you and the target you’re tracking. Each time you make a move, the path will be updated, the location of the target is obtained silently through a bypass made in the browsers, allowing you to skip the location request on the victim’s side, and at the same time maintain a precision of 99% in the locator.
- One of its most enticing functions is the remote recognition of sessions. You can know where a person has logged in, remotely. This occurs through a Bypass made to the Same Origin Policy (SOP)
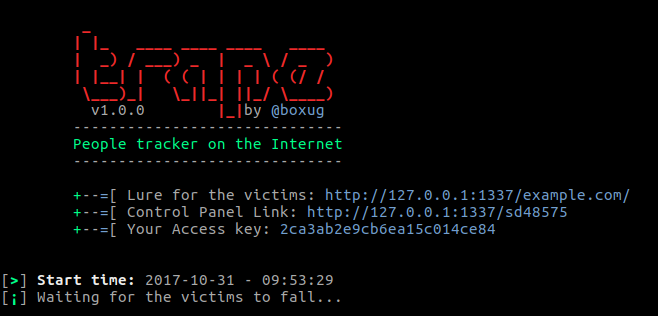
Currently you can try everything from a web interface. (The console, becomes a preview of the logs and actions) - Registration of victims, requests among other data are obtained in real time.
If you get more information from a person behind a computer, you can generate a more direct and sophisticated attack. - You can do real time phishing attacks
- Simple hooking attacks
- Mapping
Read Also: Private Internet Access – Most Popular VPN
Session recognition is one of trape most interesting attractions, since you as a researcher can know remotely what service the target is connected to.

Installation and Usage
First of all – you need to unload the tool.
git clone https://github.com/jofpin/trape.git
cd trape
python2 trape.py -hIf it does not work, try to install all the libraries that are located in the file requirements.txt
python2 -m pip install -r requirements.txtExample of execution
python2 trape.py --url http://example.com --port 8080Help and options
securityland:~$ python2 trape.py --help
usage: python trape.py -u <> -p <> [-h] [-v] [-u URL] [-p PORT]
[-ak ACCESSKEY] [-l LOCAL]
[--update] [-n] [-ic INJC]
optional arguments:
-h, --help show this help message and exit
-v, --version show program's version number and exit
-u URL, --url URL Put the web page url to clone
-p PORT, --port PORT Insert your port
-ak ACCESSKEY, --accesskey ACCESSKEY
Insert your custom key access
-l LOCAL, --local LOCAL
Insert your home file
-n, --ngrok Insert your ngrok Authtoken
-ic INJC, --injectcode INJC
Insert your custom REST API path
-ud UPDATE, --update UPDATE
Update trape to the latest versionDisclaimer
This tool has been published educational purposes. Trape creators said that they are totally convinced that if all of us teach how vulnerable things really are, we can make the Internet a safer place.